User Lifecycle Management
Active Directory Management & Automation
At 01LOGIX, we harness our extensive experience and strategic partnerships with industry leaders such as Microsoft and Softerra, along with proprietary in-house tools, to craft and deploy comprehensive ULM solutions tailored to your IT department’s needs. By adhering to best practices and innovative approaches, we empower organizations to streamline their ULM processes, thereby enhancing user experiences for employees and contractors alike. Our expertise enables IT departments to optimize resource allocation, fortify their security infrastructure, boost operational efficiency, and align seamlessly with overarching business objectives.
User Lifecycle Management (ULM)
User lifecycle is the term that describes the stages of a user’s relationship with an organization, from the moment they join until the moment they leave. It involves various processes and tasks that are performed by the IT department to ensure that users have secure and efficient access to the applications and resources they need to perform their roles. User lifecycle management (ULM) is the practice of automating and streamlining these processes and tasks, using tools and policies that can create, update, suspend, or delete user accounts and permissions across different systems and platforms. ULM can help IT departments reduce costs, improve security, enhance productivity, and comply with regulations.
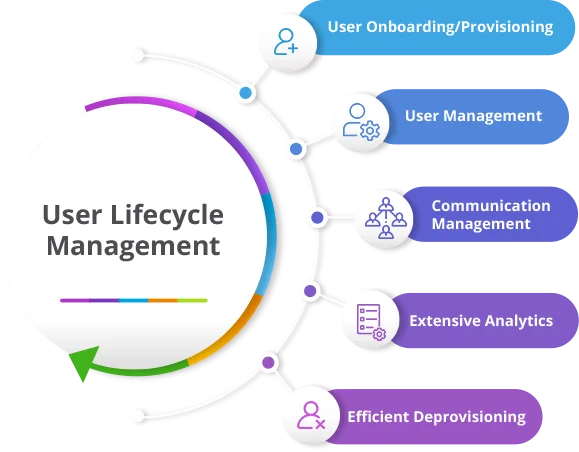
Some of the common ULM processes include:
- User provisioning: The process of creating and assigning user accounts and access rights to new employees or contractors, based on their roles and responsibilities.
- User authentication: The process of verifying the identity of users who attempt to access applications and resources, using methods such as passwords, tokens, biometrics, or multifactor authentication.
- User authorization: The process of granting or denying access to specific applications and resources, based on the user’s role, location, device, time, or other criteria.
- User management: The process of updating or modifying user accounts and access rights, based on changes in the user’s role, status, location, device, or other factors.
- User deprovisioning: The process of removing or disabling user accounts and access rights when a user leaves the organization or changes roles, to prevent unauthorized access or data leakage.
ULM can be challenging for IT departments due to the complexity and diversity of applications and resources that users need to access, as well as the dynamic nature of user roles and needs. Therefore, IT departments should adopt best practices and solutions that can simplify and automate ULM processes, such as:
- Using a single identity provider (IdP) that can integrate with multiple applications and resources, and provide a centralized platform for managing user identities and access rights.
- Implementing a role-based access control (RBAC) model that can define user roles and permissions based on their functions and responsibilities, rather than individual attributes or preferences.
- Leveraging a ULM solution that can connect to various cloud and on-premises applications and resources, and provide scalability, flexibility, and security for ULM processes.
- Enforcing a strong password policy that can require users to create complex and unique passwords, change them regularly, and use multifactor authentication when possible.
- Conducting regular audits and reviews of user accounts and access rights, to identify and resolve any issues or discrepancies that may compromise security or compliance.
User Lifecycle within IT
Using Human Resource Management System (HRMS) as the Single Source of Truth (SSOT).
Most organizations consider their HRMS as the single source of truth (SSOT) in their user lifecycle management process. This means that the HR department will be responsible for creating, updating, and deleting user accounts and permissions across all systems and applications. HR ensures that user data is accurate, consistent, and secure throughout the user lifecycle, from onboarding to offboarding. By using HR as SSOT, an organization can streamline user management processes, reduce errors and risks, and improve compliance and auditability.
We deploy our AD Linked software to connect your HR system and the on-premises Active Directory. All provisioning, deprovisioning and user updates will be directly based on HR department’s actions within the HRMS.
Active Directory Management
Active Directory Management is the process of administering and maintaining the directory service that stores information about users, computers, groups, and other objects on a network. Active Directory Management involves tasks such as creating and deleting accounts, assigning permissions and roles, configuring policies and settings, and monitoring performance and security.
As a Softerra partner, we deploy Adaxes, an Active Directory automation software, and design and implement the following:
- Deploy a rule-based platform for Active Directory, Azure AD, Exchange, and Microsoft 365 automation.
- Provide an enhanced web-based management environment.
- Implement a role-based access control model for delegating privileges.
- Add security with approval-based workflows, allowing enforcement of corporate data standards.
Automated Provisioning
By establishing the HR system as the single source of truth (SSOT), fully automate all user lifecycle management procedures, including provisioning, re-provisioning and deprovisioning in Active Directory and connected systems, such as Azure AD, Exchange and Microsoft 365 and other business system that make use of Active Directory as a source.
Role-Based Delegation
Deploy a Role-Based Access Control model following the least privilege principle. Provide a centralized control over permissions which can be delegated, managed and revoked efficiently.
Single Interface for AD, Exchange, and Microsoft 365
Deploy a Web Interface for all Active Directory, Exchange and Microsoft 365 tasks combined into a single place, providing a simple and elegant management experience, eliminating the need for users to learn multiple tools and switch between them in day-to-day routines.
Approval-Based Workflow
Adding approval steps to practically any operation in your Active Directory environment. Such approach allows delegating more responsibilities to lower-level staff without losing control or adding any security risks.
Self-Password Reset
Provide a Password Self-Service portal eliminating the problem of resetting forgotten passwords and unlocking accounts. Allowing users to do it by themselves after they verify their identity by answering security questions and/or providing a code received via SMS, email or a mobile app (Google Authenticator, Authy, Okta Verify and others). Ability to extend the service to offsite and offline, covering users who forget their password while working from home or on business trips.
Active Directory Reports
Provide detailed reports on your Active Directory environment. In addition to the 200+ built-in ones, provide the ability to create a powerful platform for custom reports of any complexity. Supporting centralized scheduling and allowing users to schedule reports of their choice for themselves.
Key Benefits
- Reduced Workload – By automating everyday tasks, user lifecycle management, streamlined provisioning, self-service portal, web interface — all that can massively reduce the routine workload on the IT staff.
- Increased Security – Significantly increased Active Directory security due to the approval-based workflows, role-based security administration model and automated user provisioning and deprovisioning.
- Efficient Audit and Monitoring – Comprehensive tracking and reporting enabling advanced analysis and monitoring of the enterprise resources making Active Directory environment a more regulated and elaborated place.
- Standardized AD Environment – By enforcing corporate standards on Active Directory data, minimizing possible human factor mistakes and making the management process cleaner and easier.